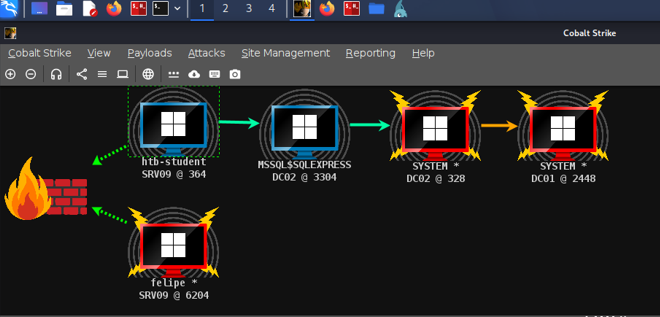
Sliver Challenge - Answered with Cobalt Strike
HTB Sliver Skill Assessment but I answered it with Cobalt Strike.
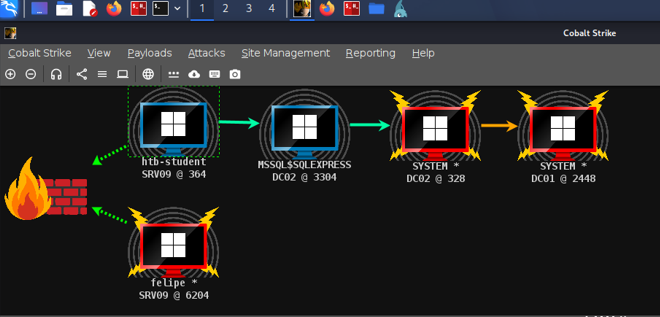
HTB Sliver Skill Assessment but I answered it with Cobalt Strike.

Project Black is an online CTF series. Challenge 6 is a multi-stage web challenge involving steganography, API exploitation, IDOR, and database forensics.
Exploiting Timing-Based Username Disclosure
NoSQL Injection to RCE via Rocket.Chat CVE-2021-22911

Identifying unconstrained, constrained, and resource-based constrained delegation in AD
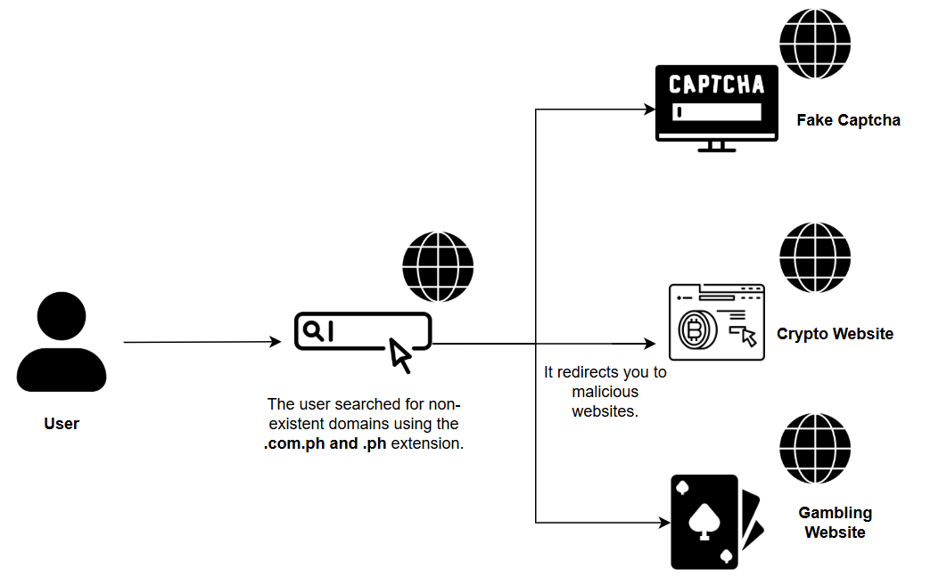
This report covers the Infostealer campaign known as the FakeCaptcha/Click-Fix Campaign. Background On March 4, 2025, an alert was triggered after a suspicious PowerShell script ran on a user’s m...

Using unshadow to combine passwd and shadow files for password cracking

Understanding how writable /etc/passwd can lead to privilege escalation

Joy is a beginner-to-intermediate level boot2root challenge hosted on VulnHub.

Detailed security assessment write-up for the Secura Lab.